Security
Sovereignty
Resilience
The event from the ICT sector,
for the ICT players
- November 17 & 18, 2026
- A LU-CIX event hosted at the Luxembourg Chamber of Commerce
- 13th edition
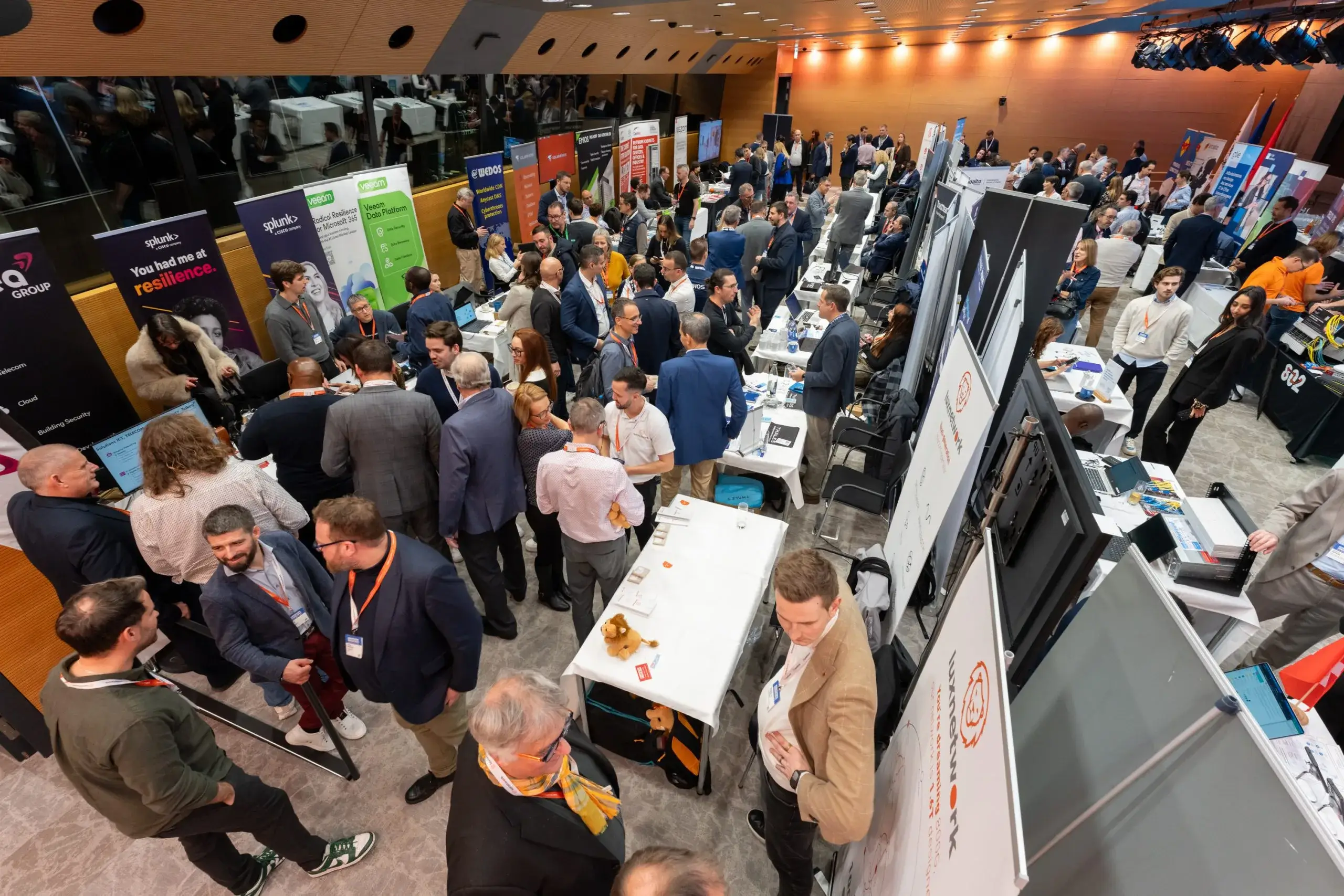
On Nov. 17 & 18, 2026, over 1,300 experts, ICT decision-makers, CTOs, CISOs, and business leaders are expected to join conferences and visit the 47-booth Expo area.
Attendees will share insights on their key challenges, including anticipating evolving security risks, implementing corrective measures, and identifying top solutions—all while balancing board priorities with NIS2 Directive compliance.
We will also explore AI and Open-source opportunities regarding IT security, risk management and sovereignty.
KEY FACTS
- 1.700 professionals and experts registered
- Over 40 focus conferences and interactive workshops
- An Expo with 47 stands
- The Internet and Technology event-to-be in the Greater Region
- Meet with key sector experts
- Network with peers and make new contacts
- Find new solutions to your challenges


1 place, 2 days and 3 events to fit different types of attendees
Join us in March 2027 for the second edition of our HACKATHON Luxchat(4GOV)!
New collaborations, new creative projects and new exciting challenges are to come.
Stay tuned for more information in the coming months.
ADVISORY BOARD 2026
LU-CIX has gathered a team of key sector experts and users, aware of Internet related challenges, trends and hot topics to help propose the best solution-oriented event to its attendees.
ASSOCIATES PARTNERS 2026
Want to have visibility?
Discover all our sponsorship packages to promote your company during the event.
FREQUENTLY
ASKED
QUESTIONS
How much is the entry of the event?
The entry of the event is free of charge for everyone. You just need to register online.
What is the language of the event?
The official language of the event is English, except for the Gemengen Dag (French/Luxembourgish).
Is it the same registration for all the side events?
Yes, it is the same registration for the Luxembourg Internet Days and all its side events.
When will the programme be available?
The programme of the event will be available in October.
How to become a sponsor?
Check out our sponsorship packages here and click on “Book now” to download the booking form.
How to access the event platform (Swapcard)?
The platform will open in October.
Who is the organiser of the Luxembourg Internet Days?
The organiser is LU-CIX, the LUxembourg Internet Exchange.